Protect your WordPress Login against Brute-Force Attack for customers with SolidCP
The solution described below (applies for all customers with SolidCP based hosting accounts) will provide you with an additional password for your wp-login page, thus increasing your defense against brute force attacks significantly.
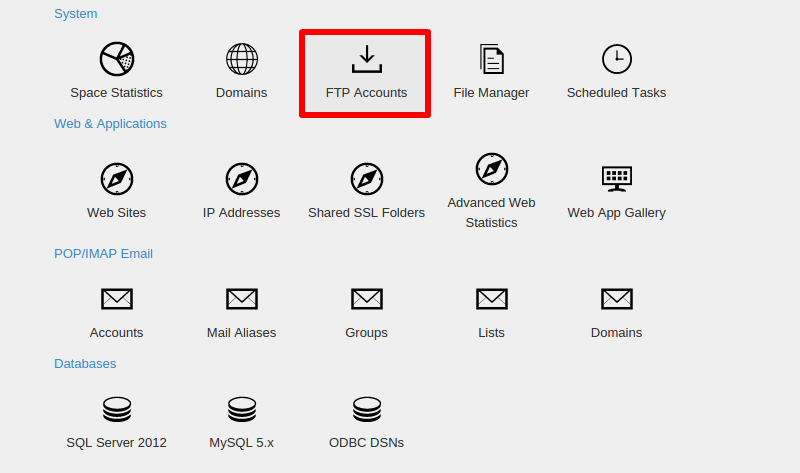
1. Log in into your control panel
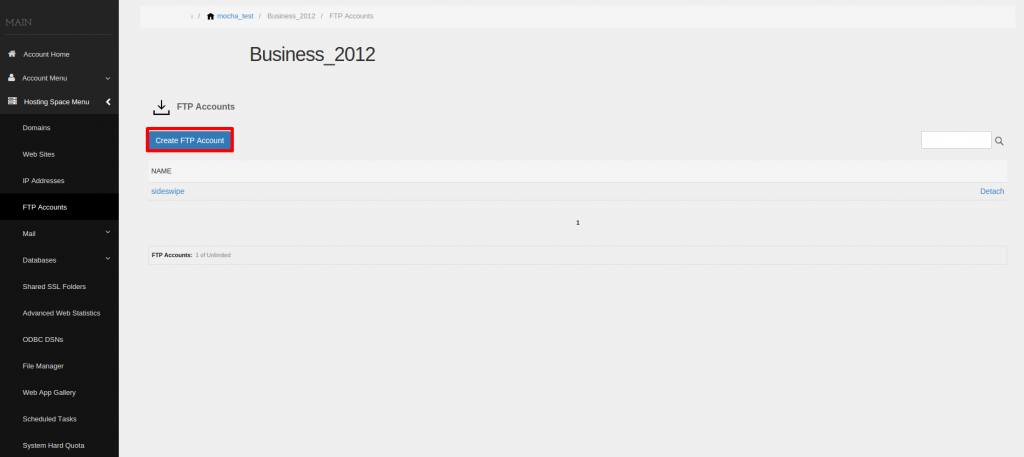
2. Create a FTP account that will be used mainly for access to WordPress. From the menu that will be shown above, click on ‘Create FTP Account’.
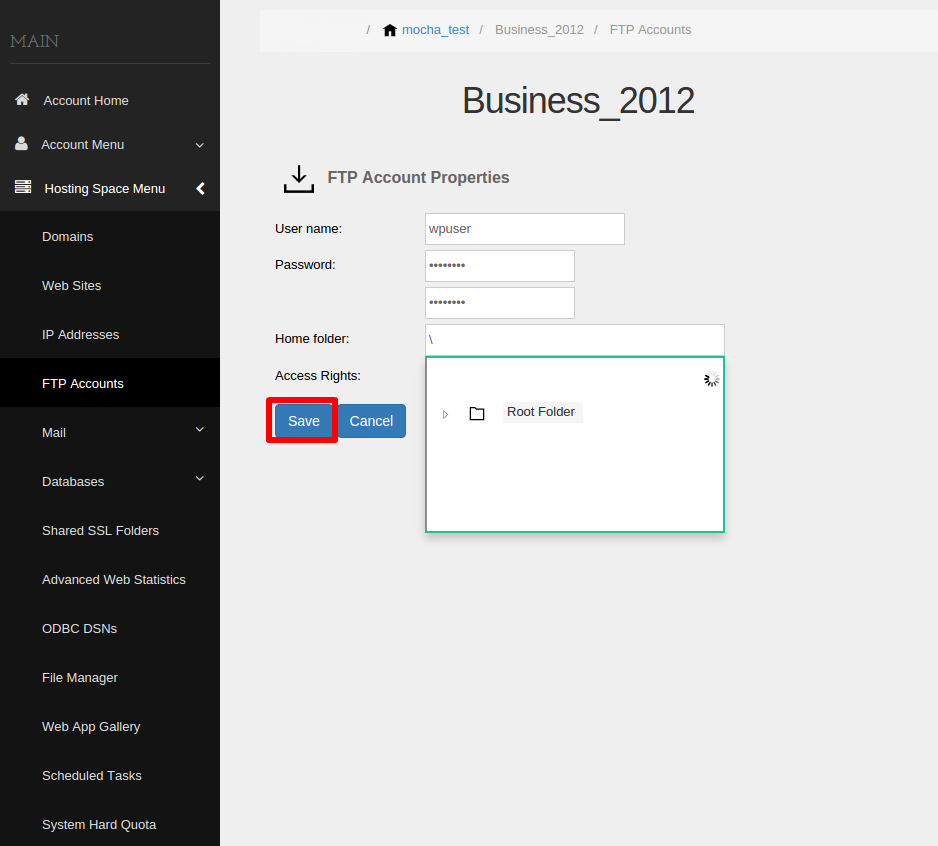
3. Create the user and its login credentials, as well as define the path to which this user will have access from the tree hierarchy. Make sure that you follow all the tips on how to create a good password when choosing the login credentials.
4. Once created, you will be able to see the user in the FTP account section of your control panel. Now navigate to your File Manager
5. Once in the file manager, choose the domain for which you want to protect the wp-login
6. Using the tree hierarchy, navigate to the folder in which the WordPress is installed and click on the web.config file
7. If the file does not exist, then you should create it. Once opened you should set this code
<?xml version="1.0" encoding="UTF-8"?>
<configuration>
<location path="wp-login.php">
<system.webServer>
<security>
<authentication>
<anonymousAuthentication enabled="false" />
<basicAuthentication enabled="true" />
</authentication>
</security>
</system.webServer>
</location>
</configuration>
If the file is empty, you should add this text. However, if the file has already been created, overwrite the existing information with the code above.
Now try to login to your WordPress login page. You should be asked for user and password. Once you enter the login credentials you have just created in your SolidCP Panel, you will be forwarded to your login page.
That’s it! You have just created an additional shield to your WordPress site.
Note: Keep in mind that all users who have access to this directory or to any parent directory, will also have access to this login page.
Yours,
MH Support Team